Multi Layered Security Solutions: Because One Lock is Never Enough
Why One Lock Is Never Enough: The Case for Multi Layered Security Solutions
Multi layered security solutions — also called defense in depth — are the practice of stacking multiple independent security controls so that if one fails, others still protect you.
Quick answer: What are multi layered security solutions?
Layer What It Does Example Tools Perimeter Blocks threats at the edge Firewalls, IDS/IPS Network Protects data in transit TLS, VLANs, segmentation Endpoint Secures every device EDR, antivirus, MDM Application Hardens software WAF, secure coding, API security Data Protects sensitive information Encryption, DLP, backups Identity Controls who gets in MFA, IAM, least privilege Human Reduces human error Security training, phishing simulations
No single tool stops every attack. Cybercriminals today use multi-stage tactics — starting with a phishing email, stealing credentials, then moving laterally until they reach your most sensitive data. A firewall alone won't catch all of that. Neither will antivirus software on its own.
Think of it like a bank vault. One lock on the front door isn't enough. You need cameras, access cards, a timed lock, guards, and alarms — each one backing up the others if something slips through.
For organizations in healthcare, defense, or finance, the stakes are even higher. A single breach can mean HIPAA violations, CMMC audit failures, or massive fines — on top of the operational damage.
I'm Michael Gaigelas II, and I've spent my career guiding regulated organizations through exactly this challenge — building and implementing multi layered security solutions that satisfy CMMC 2.0, HIPAA, ISO 27001, and SOC 2 requirements without blowing the budget. In this guide, I'll walk you through how to build a defense-in-depth strategy that actually works.
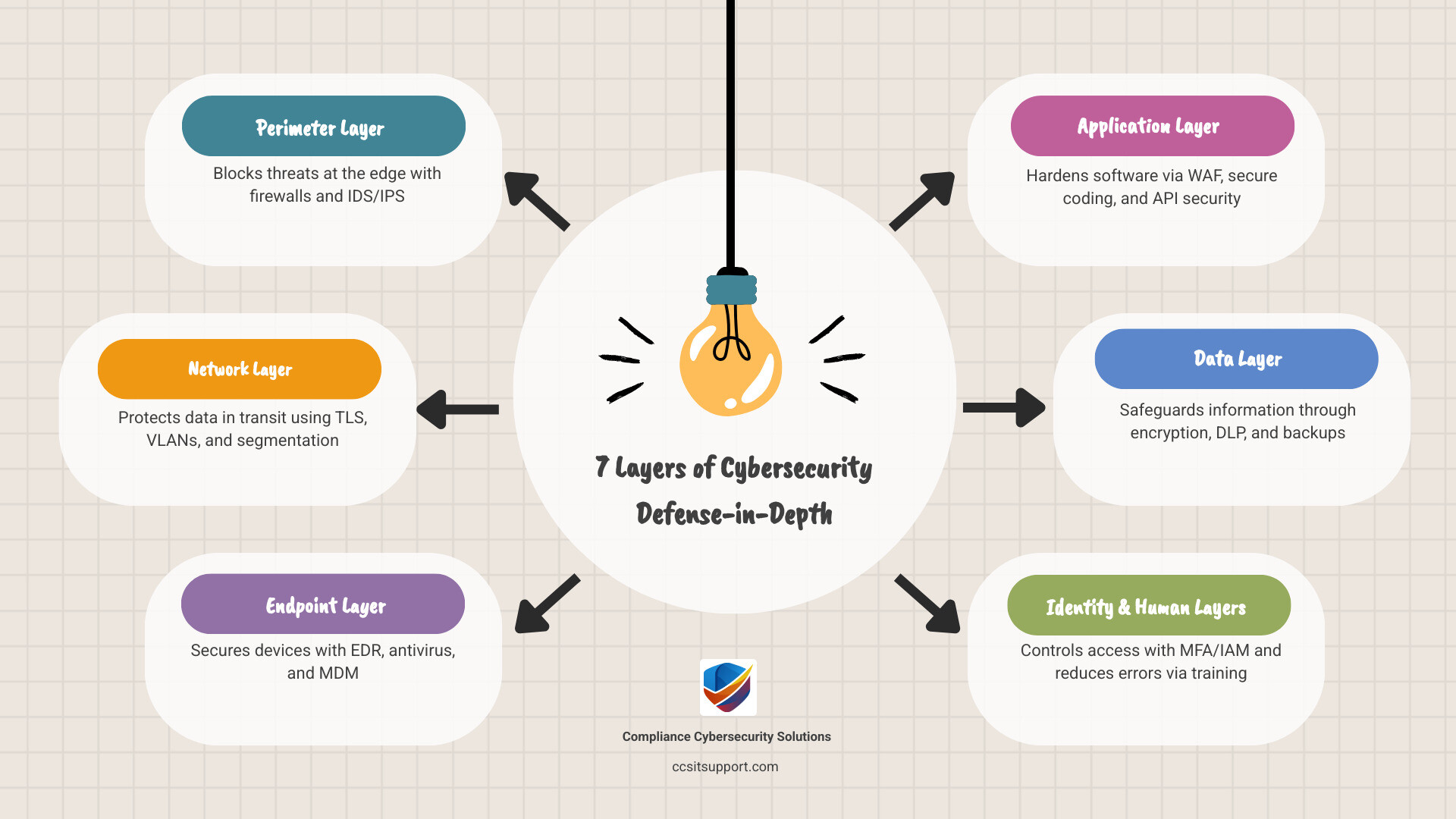
The Core Components of a Multi Layered Security Strategy
When we talk about building a resilient defense, we aren't just buying more software. We are creating a "gauntlet" that attackers must run. If they pick one lock, they find another door. If they climb a wall, they fall into a pit. In technical terms, we call this redundancy.
A comprehensive cybersecurity strategy involves looking at your entire digital footprint and placing barriers at every possible entry point. This includes your office's physical front door, the Wi-Fi in the breakroom, the laptops your remote team uses, and the cloud servers where your patient or financial data lives.
Perimeter Security: The First Line of Defense
Perimeter security is all about keeping the "bad guys" out of the "good place." Traditionally, this meant a firewall, but modern multi layered security solutions go much further. We now use Secure Gateways to filter web traffic and reduce the attack surface by hiding internal resources from the public internet.
In high-stakes environments, perimeter defense even extends to the physical world. Technologies like active infrared beams and LiDAR detection create "invisible walls" around critical infrastructure. If an intruder attempts to physically access a server room in a Florida data center, these systems trigger automated responses—turning on cameras or locking down digital access points before the intruder even reaches a keyboard.
Network Security: Safeguarding Data Transmission
Once someone is "inside" the network (whether they are a legitimate employee or a clever hacker), network security takes over. We don't want a "flat" network where a breach in the guest Wi-Fi leads straight to the payroll server.
Network Segmentation & VLANs: We break the network into smaller, isolated pieces. This limits "lateral movement," ensuring that if one segment is compromised, the rest remain safe.
Secure Protocols: We enforce HTTPS/TLS for all data moving across the wire.
Vulnerability Management: We perform regular research and scans to find unpatched holes in the network before attackers do.
Endpoint Security: Protecting Every Device
Endpoints—laptops, smartphones, and tablets—are often described as "transcendental" in a security strategy because they move in and out of your protected perimeter. Every device is a potential target.
To protect them, we move beyond basic antivirus. We deploy Endpoint Detection and Response (EDR), which uses behavioral AI to spot suspicious activity, like a Word document suddenly trying to encrypt files. We also use Mobile Device Management (MDM) to ensure that if a tablet is lost in a South Florida coffee shop, we can wipe the data remotely before it falls into the wrong hands.
Strengthening the Human and Identity Layers
Identity is the new perimeter. In a world of remote work and cloud apps, "where" you are matters less than "who" you are. If an attacker steals a valid username and password, they don't need to "hack" in—they just log in.
Implementing Multi Layered Security Solutions for Identity
We follow the Principle of Least Privilege, meaning users only get access to the specific data they need to do their jobs. No more, no less.
Multi-Factor Authentication (MFA): This is the single most effective tool in your kit. Research shows that MFA can block over 99.9% of account compromise attacks. Even if a hacker has a password, they won't have the physical token or biometric scan needed to finish the job.
Single Sign-On (SSO) & Adaptive Authentication: SSO reduces "password fatigue" (and the temptation to write passwords on sticky notes), while adaptive authentication looks for "impossible travel"—like a user logging in from Fort Lauderdale and then two minutes later from another continent.
The Human Layer: Security Awareness and Culture
The most sophisticated software can't stop an employee from handing over their password to a convincing "IT guy" on the phone. Since 76% of cyber insurance claims in 2024 originated as phishing attempts, the human layer is your most critical—and often weakest—defense.
We help organizations build a "report, don't ignore" culture. This involves regular phishing simulations and security awareness training. When employees know how to spot vulnerabilities and social engineering tactics, they transform from a liability into a powerful human firewall.
Protecting the Crown Jewels: Data and Application Security
At the end of the day, hackers want your data. Whether it's protected health information (PHI) or intellectual property, we must protect it both while it's sitting on a drive and while it's moving across the internet.
Protection Type Data at Rest (Stored) Data in Transit (Moving) Primary Goal Prevent unauthorized access to stored files Prevent "eavesdropping" during transfer Key Tech AES-256 Encryption, Full-Disk Encryption TLS 1.3, SSL, VPNs Monitoring File Integrity Monitoring (FIM) Network Sniffing Detection Control Data Loss Prevention (DLP) Secure Protocols (HTTPS)
Application Security: Hardening the Software Layer
Your software shouldn't trust its own code. We implement Web Application Firewalls (WAF) to block Layer 7 attacks, such as SQL injection or Cross-Site Scripting (XSS), which target the "OWASP Top 10" vulnerabilities. We also recommend penetration testing to find the gaps in your custom applications before a malicious actor does. Following the National Institute of Standards and Technology (NIST) framework ensures that your application security aligns with global best practices.
Data Resilience: Backups and Recovery
No security is 100% foolproof. That’s why multi layered security solutions must include a "Plan B." If ransomware manages to slip through, your last line of defense is your backup system.
We don't just back up data; we ensure it is "immutable" (cannot be changed or deleted by the ransomware) and stored off-site. A robust compliance strategy requires not just having backups, but testing them regularly to ensure you can actually recover in hours, not weeks.
Implementing Multi Layered Security Solutions in Cloud and Hybrid Environments
The cloud has changed everything. You no longer own the "hardware," but you still own the "risk." Under the Shared Responsibility Model, cloud providers protect the infrastructure, but you are responsible for securing the data and identities inside it.
AI-Powered Detection and Continuous Monitoring
Modern threats move at "machine speed," using AI to find vulnerabilities in seconds. To fight back, we use AI-powered multi layered security solutions.
SIEM (Security Information and Event Management): This acts as the "brain" of your operation, collecting logs from every layer—firewalls, endpoints, and cloud apps—to find patterns that a human would miss.
Behavioral Analysis: Instead of looking for known "viruses," these tools look for weird behavior. If a server that normally sends 10MB of data suddenly tries to send 10GB to an unknown IP address, the system shuts it down automatically.
Maintaining Compliance in Regulated Industries
For our clients in Florida and across the US, security isn't just a good idea—it's the law. Whether you are dealing with HIPAA in healthcare, CMMC in defense contracting, or PCI-DSS in finance, your security layers must be documented and auditable. We align your IT infrastructure with these frameworks, ensuring that your support center is always ready for an unexpected audit.
Measuring Success and Overcoming Implementation Challenges
You can't manage what you can't measure. Building a multi-layered defense can feel overwhelming, and "alert fatigue" is a real danger. If your team gets 1,000 notifications a day, they will eventually miss the one that actually matters.
Best Practices for Deploying Multi Layered Security Solutions
To avoid complexity creep, we focus on integration. Your tools should talk to each other. When your EDR spots a threat on a laptop, it should automatically tell the firewall to block that device's access to the rest of the network.
Key metrics we track include:
Mean Time to Detect (MTTD): How long does it take us to know we've been hit?
Mean Time to Respond (MTTR): How fast can we neutralize the threat?
Containment Rate: Can we stop the attack at the first "hop" before it spreads?
By prioritizing risks and conducting regular security audits, we ensure your budget is spent where it makes the most impact. Check out our resources for more on building a sustainable IT strategy.
Frequently Asked Questions about Multi Layered Security
What is the difference between layered security and defense in depth?
While often used interchangeably, "layered security" usually refers to the specific technical tools (firewall + antivirus + encryption). "Defense in depth" is the broader strategy that includes those tools plus people (training), processes (policies), and physical security.
How does multi-layered security protect against ransomware?
It creates a "gauntlet." The email filter stops the phishing link. If the link is clicked, the endpoint protection blocks the malware execution. If the malware runs, network segmentation prevents it from reaching the server. If it reaches the server, data encryption and backups ensure you don't have to pay the ransom to get your files back.
Why is physical security considered a layer of cybersecurity?
Because if a thief can walk into your office and steal a backup drive or plug a "bad USB" into a server, your digital firewalls don't matter. Physical access is the ultimate administrative bypass.
Conclusion
In the modern threat landscape, relying on a single security tool is like putting a $500 lock on a cardboard door. Multi layered security solutions provide the redundancy and resilience needed to protect your business from sophisticated, AI-driven attacks.
By stacking defenses across your perimeter, network, endpoints, and—most importantly—your people, you create a system where no single failure leads to a catastrophe. At Compliance Cybersecurity Solutions (CCS), we specialize in making these complex strategies simple and affordable for regulated industries.
Don't wait for a breach to find the holes in your defense. Contact us for multi-layered security solutions today, and let's build a gauntlet that keeps your data safe and your business compliant.