The Complete Healthcare Network Security Assessment Guide
Why HIPAA Cybersecurity Best Practices Matter for Healthcare Organizations
HIPAA cybersecurity best practices are the foundation every healthcare organization needs to protect patient data, avoid costly penalties, and pass compliance audits.
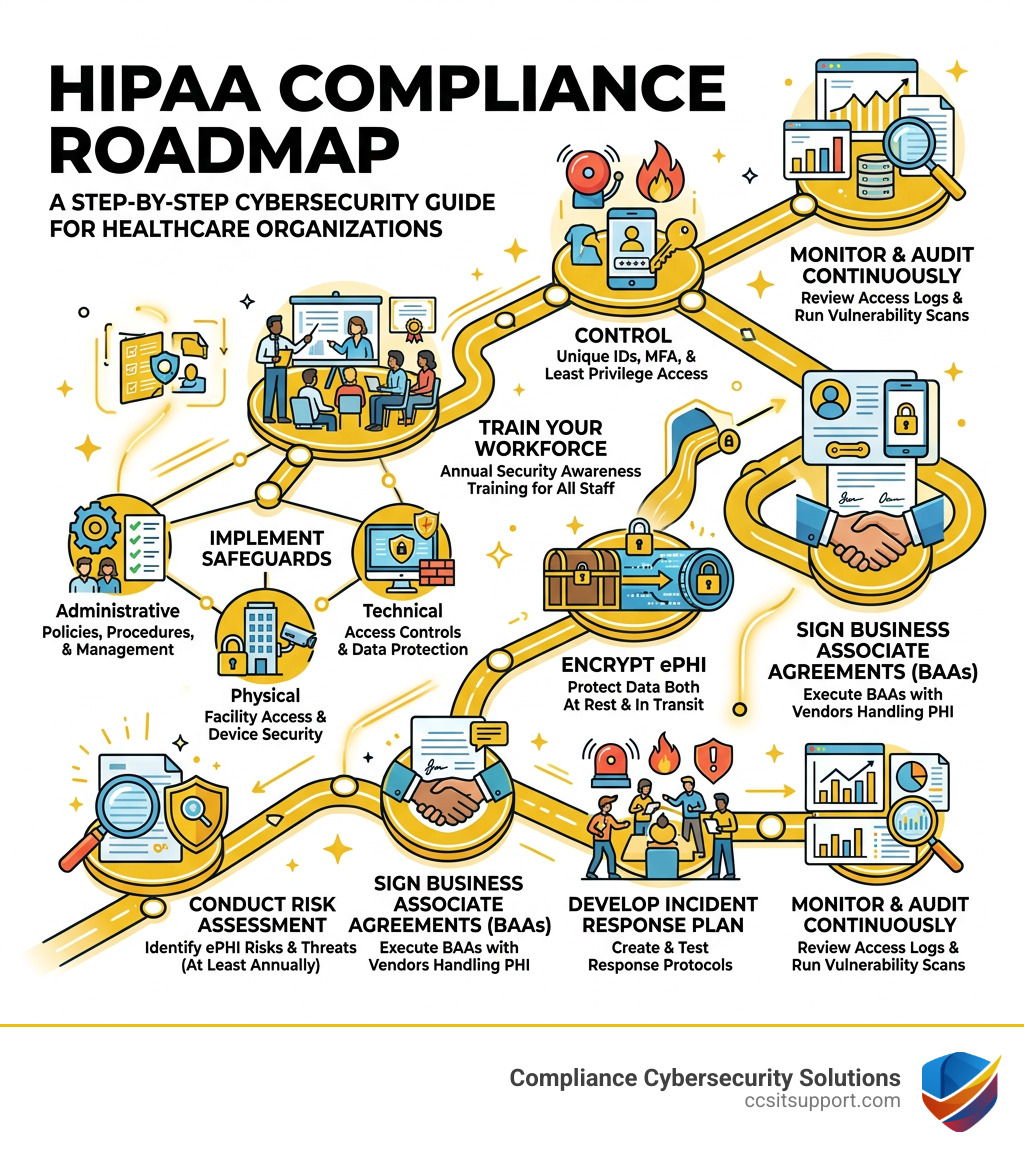
Here is a quick overview of the core practices:
Conduct a risk assessment - Identify threats to electronic protected health information (ePHI) at least annually
Implement the three safeguards - Administrative, physical, and technical controls for ePHI
Train your workforce - Annual security awareness training for all staff
Control access to ePHI - Use unique user IDs, multi-factor authentication, and least privilege
Encrypt ePHI - Both at rest and in transit
Sign Business Associate Agreements (BAAs) - With every vendor that handles PHI
Develop an incident response plan - And test it regularly
Monitor and audit continuously - Review access logs and run vulnerability scans
Healthcare is one of the most targeted industries for cyberattacks. Ransomware, phishing, and insider threats hit hospitals, clinics, and their vendors every day. The stakes are high: HIPAA violations can cost anywhere from $100 to $50,000 per violation, with annual caps reaching $1.5 million for repeat offenses — plus potential criminal charges on top of that.
And yet many organizations still treat compliance as a checkbox rather than an ongoing security program. That gap is exactly where breaches happen.
Whether you run a small medical practice or a large health system, the HIPAA Security Rule applies to you. This guide breaks down what you need to do — and how to actually do it.
I'm Michael Gaigelas II, and I've guided hundreds of regulated businesses through HIPAA cybersecurity best practices as part of broader compliance frameworks including CMMC 2.0, ISO 27001, and SOC 2. My focus is always on efficient, cost-effective security — helping organizations achieve compliance faster without unnecessary overhead or surprise costs.
The Three Pillars of the HIPAA Security Rule
To understand how to protect your organization, we first need to look at the Health Insurance Portability and Accountability Act (HIPAA) standards. The Security Rule specifically focuses on Electronic Protected Health Information (ePHI). This is any identifiable health information that is stored or sent in digital form.
Under HIPAA, there are two types of entities that must comply:
Covered Entities (CE): Healthcare providers, health plans, and healthcare clearinghouses.
Business Associates (BA): Third-party vendors (like IT providers, cloud storage, or billing companies) that create, receive, maintain, or transmit ePHI on behalf of a Covered Entity.
The Security Rule is built on three pillars of safeguards:
1. Administrative Safeguards
These are the "brains" of your compliance program. They include the policies and procedures that manage your selection, development, and implementation of security measures. Key requirements include designating a Security Officer, performing regular risk analyses, and implementing workforce training.
2. Physical Safeguards
You can have the best firewall in the world, but it doesn't matter if someone can walk into your office and steal a server. Physical safeguards involve limiting access to facilities and protecting workstations and mobile devices from unauthorized physical access or theft.
3. Technical Safeguards
These are the technology-driven defenses. They focus on the software and hardware that protect ePHI and control access to it. This includes encryption, audit controls, and integrity measures to ensure data isn't altered or destroyed in an unauthorized manner.
HIPAA Violation Penalties
Ignoring these pillars is a recipe for financial disaster. Fines for HIPAA violations are tiered based on the level of negligence. They range from $100 to $50,000 per violation, but the real sting comes from the annual cap of $1.5 million for repeat violations. Furthermore, severe violations can lead to civil or criminal litigation, and the FTC can levy additional fines for breach notification failures—up to $46,517 per day.
Required vs. Addressable Specifications
A common point of confusion is the difference between "Required" and "Addressable" implementation specifications. "Required" means you must do it. "Addressable" doesn't mean "optional." It means you must assess if the measure is reasonable and appropriate for your environment. If it isn't, you must document why and implement an equivalent alternative.
Standard Category Implementation Specification Type Administrative Risk Analysis Required Administrative Sanction Policy Required Physical Facility Security Plan Addressable Physical Device and Media Controls Required Technical Encryption and Decryption Addressable Technical Automatic Logoff Addressable
Essential HIPAA cybersecurity best practices for ePHI Protection
Implementing HIPAA cybersecurity best practices isn't just about passing an audit; it's about building a resilient defense against modern threats. As we provide cybersecurity services in Florida, we've seen that the most successful organizations focus on these core technical areas:
Multi-Factor Authentication (MFA): This is no longer a luxury; it's a necessity. MFA adds a layer of protection so that even if a password is stolen, the attacker cannot access ePHI without the second factor (like a code from an app).
Data Encryption: You should encrypt ePHI "at rest" (while it's sitting on a hard drive or cloud server) and "in transit" (while it's being emailed or sent over the internet). If encrypted data is stolen, it remains unreadable to the thief.
System Hardening: This is the process of securing a system by reducing its surface of vulnerability. This includes changing default passwords, disabling unnecessary services (like RDP or Telnet), and removing "bloatware" that comes pre-installed on devices.
Vulnerability Management: We recommend monitoring the NIST National Vulnerability Database (NVD) and CISA’s Known Exploited Vulnerabilities Catalog. Regularly patching your operating systems, firmware, and applications is critical to closing the doors that hackers use.
IT Asset Inventory: You can't protect what you don't know you have. Maintain a detailed list of every laptop, server, tablet, and medical device that touches your network.
Ransomware and Phishing Defense: Healthcare is a top target for ransomware. Beyond technical filters, you need a robust backup strategy that includes "offline" or immutable backups that attackers can't reach.
Implementing HIPAA cybersecurity best practices for Access Control
Controlling who can see patient data is a fundamental requirement. We follow these specific steps:
Unique User IDs: Never use shared accounts. Every staff member must have their own login to ensure accountability.
Least Privilege Principle: Only give employees access to the specific data they need to do their jobs. A receptionist likely doesn't need access to full surgical records.
Automatic Logoff: Devices should automatically lock or log out after a period of inactivity to prevent unauthorized access to unattended workstations.
Credential Verification: Before granting access to ePHI, always verify the identity of the person or entity requesting it.
Employee Training as a HIPAA cybersecurity best practices Pillar
Human error remains one of the leading causes of data breaches. Your staff is your first line of defense—or your weakest link.
Security Awareness: Conduct annual training that covers the basics of HIPAA and current cyber threats.
Phishing Simulations: Send "fake" phishing emails to staff to see who clicks. Use these as teaching moments rather than punishments.
Sanction Policies: HIPAA requires you to have a policy that outlines the consequences for employees who violate security policies.
Role-Based Training: Provide specialized training for IT staff or those with high-level access. We often point clients toward the NIST Special Publication 800-66 Rev. 2 guidance for deep dives into technical implementation.
Risk Management, NIST Alignment, and Incident Response
Compliance isn't a "one and done" event. It requires a continuous cycle of assessment and improvement.
The Risk Analysis
The HIPAA Security Rule requires an "accurate and thorough" risk analysis. This means identifying where ePHI is stored, what threats exist (human, natural, or environmental), and how likely those threats are to occur. While HHS doesn't mandate a specific methodology, the HHS Security Risk Assessment (SRA) Tool is a great resource for smaller practices. We recommend performing these analyses at least annually or whenever you make a significant change to your IT environment (like moving to a new EHR or opening a new office).
NIST Cybersecurity Framework Alignment
Many healthcare organizations in Florida are now aligning their HIPAA programs with the NIST Cybersecurity Framework (CSF). NIST provides a more detailed roadmap for managing cybersecurity risk. By mapping HIPAA standards to NIST controls, you can create a much more robust security posture that satisfies both regulators and insurance providers.
Incident Response and Breach Notification
If a breach does occur, the clock starts ticking immediately. Under the HIPAA Breach Notification Rule:
Individual Notification: You must notify affected individuals without unreasonable delay, and no later than 60 days after discovering the breach.
HHS Notification: If the breach affects 500 or more people, you must notify HHS and local media within that same 60-day window. If it's fewer than 500, you can report it annually.
Business Associate Agreements (BAAs): You must have a signed BAA with every vendor that handles your ePHI. This contract ensures they are also following HIPAA rules and outlines their responsibility to notify you if they have a breach.
Monitoring and Auditing
You must implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI. This means reviewing audit logs regularly to look for suspicious login attempts or unusual data access patterns.
Frequently Asked Questions about HIPAA Cybersecurity
How often should healthcare organizations conduct HIPAA risk assessments?
While the law doesn't specify a calendar timeframe (like "every 12 months"), the industry standard is to conduct a comprehensive risk assessment at least once a year. However, you must also perform an assessment whenever there is a "significant change" to your business—such as implementing new software, a security incident, or a change in physical location.
What are the potential penalties for HIPAA cybersecurity violations?
Penalties are divided into four tiers based on "culpability." They start at $100 per violation for "no knowledge" (where the entity didn't know it violated the rule) and go up to $50,000 per violation for "willful neglect" that is not corrected. Annual caps for identical violations can hit $1.5 million. Beyond fines, the Office for Civil Rights (OCR) often imposes a "Corrective Action Plan" which involves years of federal monitoring.
Do small medical practices need to comply with the HIPAA Security Rule?
Yes. HIPAA does not have a "small business exception." Whether you are a solo practitioner or a multi-state hospital system, if you handle ePHI, you must comply. However, the Security Rule does allow for "flexibility of approach," meaning a small clinic is not expected to have the same sophisticated (and expensive) systems as a massive hospital, provided they implement reasonable and appropriate alternatives to protect data.
Conclusion
Navigating HIPAA cybersecurity best practices can feel like a daunting task, especially with the threat landscape constantly shifting. However, by focusing on the three pillars of safeguards, conducting regular risk assessments, and fostering a culture of security awareness, you can significantly reduce your risk of a devastating breach.
Recent updates, such as the 2021 HITECH Amendment, even offer a "carrot" to organizations: if you can demonstrate that you've implemented "recognized security practices" (like NIST frameworks) for the 12 months prior to a breach, the OCR may reduce your fines or mitigate the severity of an audit.
At CCS Compliance & Cybersecurity Solutions, we specialize in helping Florida healthcare providers align their IT with HIPAA requirements. We don't just "check boxes"—we build layered security that protects your patients and your reputation.
If you're ready to ensure your network is truly secure, you can find more info about our compliance services or reach out to our team in Fort Lauderdale today. Let's make sure your organization is a fortress, not a target.