Keeping Vitals Safe with a Robust Healthcare Cybersecurity Policy
Why Every Healthcare Organization Needs a Strong Healthcare Cybersecurity Policy
A solid healthcare cybersecurity policy is no longer optional — it's the foundation that keeps patient data safe, clinical operations running, and your organization on the right side of the law.
Here's what a healthcare cybersecurity policy typically needs to cover:
Policy Area What It Means Regulatory Compliance Meet HIPAA, HITECH, GDPR, and NIST requirements Access Controls Multi-factor authentication, unique credentials, privileged account separation Data Protection Encrypt electronic protected health information (ePHI) at rest and in transit Risk Management Regular risk assessments, vulnerability scanning, patch management Incident Response Plans for ransomware, breaches, and service disruptions Workforce Training Ongoing cybersecurity awareness for all staff Medical Device Security Secure IoMT devices and segment them from core networks Vendor Management Enforce cybersecurity requirements on third parties and business associates
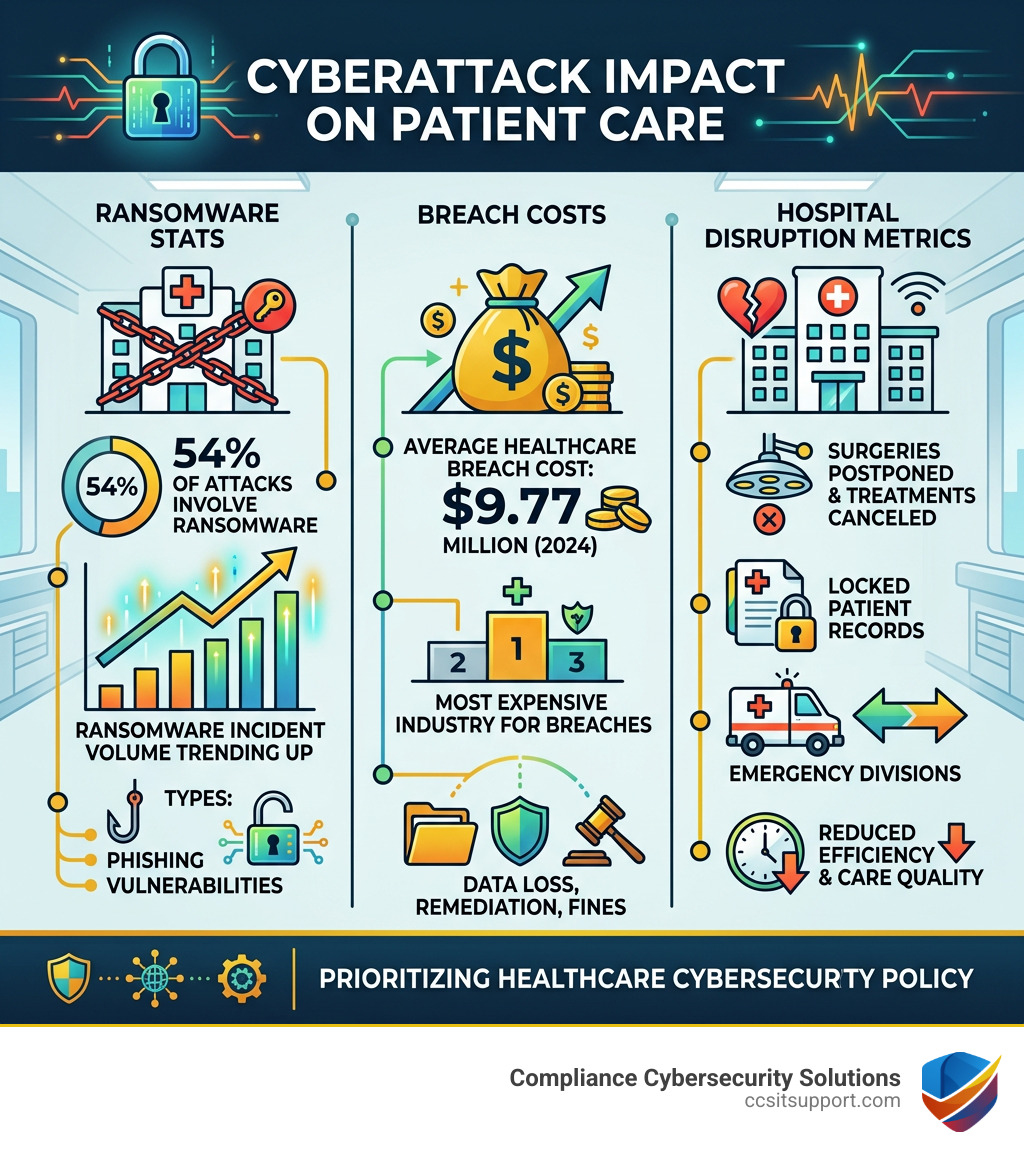
The stakes couldn't be higher. Healthcare is the most expensive industry for data breaches — averaging $9.77 million per incident in 2024. And 54% of cyberattacks on healthcare organizations involve ransomware, which can halt surgeries, lock patient records, and divert emergency patients to other facilities.
The 2017 WannaCry ransomware attack is a stark reminder of what's possible: hospitals worldwide were forced to postpone surgeries and cancel treatments because their systems were frozen. That kind of disruption doesn't just cost money — it costs lives.
I'm Michael Gaigelas II, and I've spent my career helping organizations navigate complex compliance landscapes — including healthcare cybersecurity policy — through practical, cost-effective strategies that align security with business goals. This guide will walk you through exactly what you need to build, strengthen, or audit your organization's cybersecurity policy.
The Critical Need for a Modern Healthcare Cybersecurity Policy
In medicine, we often talk about "preventative care." A healthcare cybersecurity policy is essentially preventative care for your digital infrastructure. Without it, your organization is essentially walking into a flu season without a vaccine—only the "flu" in this case is a ransomware variant that wants to hold your patient records hostage for millions of dollars.
The healthcare sector is a prime target for cybercriminals for several reasons. First, medical records are a goldmine. On the dark web, a single medical record can sell for anywhere from $250 to $1,000. Why? Because unlike a credit card number that can be canceled in seconds, a medical record contains a permanent cocktail of personal identifiers, insurance details, and financial data that can be used for identity theft and insurance fraud for years.
The Rising Tide of Breaches
The numbers are sobering. According to HIPAA Journal breach statistics, there was a 93% increase in large data breaches reported to the HHS Office for Civil Rights (OCR) between 2018 and 2022. Even more alarming is the 278% increase in breaches involving ransomware during that same period.
When a breach occurs, the fallout is devastating. Beyond the staggering average cost of $9.77 million, there are operational costs that are harder to quantify but easier to feel. We’re talking about diverted ambulances, canceled cancer treatments, and clinicians forced to use pen and paper because the Electronic Health Record (EHR) is encrypted by a hacker.

At Compliance Cybersecurity Solutions (CCS), we see these risks every day. We provide specialized cybersecurity services designed to catch these threats before they become headlines. Whether it’s phishing attempts—which are the entry point for a massive portion of attacks—or sophisticated social engineering, your policy must be the first line of defense.
Navigating the Regulatory Landscape: HIPAA, HITECH, and Beyond
If you feel like you’re drowning in an alphabet soup of regulations, you aren't alone. Between HIPAA, HITECH, and NIST, the compliance requirements for a healthcare cybersecurity policy can feel overwhelming. However, these aren't just "red tape"—they are the blueprints for a resilient organization.
The HIPAA Security Rule
The cornerstone of U.S. healthcare security is the HIPAA Security Rule, found in 45 CFR Part 160 and Part 164. It focuses specifically on Electronic Protected Health Information (ePHI) and mandates three types of safeguards:
Administrative Safeguards: These are the "brain" of your security. They include things like performing regular risk analyses, designating a security official, and ensuring your workforce is trained.
Physical Safeguards: This is about protecting the "body" of your data. Think facility access controls, workstation security, and making sure no one can just walk off with a thumb drive containing thousands of patient records.
Technical Safeguards: These are the digital locks. This includes access controls, audit logs (to see who accessed what), and transmission security to protect data as it travels across the internet.
Comparing Standards: HIPAA vs. GDPR vs. SOC 2
While HIPAA is the baseline for many in Florida, organizations dealing with international patients or seeking higher levels of trust often look at other frameworks.
Requirement HIPAA GDPR SOC 2 Primary Focus Protected Health Info (PHI) Personal Data of EU Residents Security, Availability, Integrity Mandatory? Yes (for covered entities) Yes (if handling EU data) Voluntary (but often requested) Risk Assessment Required annually Required (DPIA) Required for Trust Criteria Breach Notification Within 60 days Within 72 hours Defined by contract/standard
The HITECH Act further tightened these screws by increasing penalties for non-compliance and extending direct liability to "Business Associates"—those third-party vendors who handle data on your behalf.
To bring order to the chaos, many organizations adopt the NIST Cybersecurity Framework. It’s a flexible, scalable model that helps you Identify, Protect, Detect, Respond, and Recover. At CCS, we specialize in compliance services that align your existing IT setup with these rigorous standards, ensuring you don't just meet the "letter of the law," but actually improve your security posture.
Implementing Essential and Enhanced Healthcare Cybersecurity Policy Goals
The Department of Health and Human Services (HHS) recently released a set of Cybersecurity Performance Goals (CPGs) specifically for the healthcare sector. These are essentially the "greatest hits" of security practices, categorized into "Essential" and "Enhanced" goals.
Essential Goals: The "Must-Haves"
Your healthcare cybersecurity policy should prioritize these HHS Essential Goals as the absolute baseline:
Mitigate Known Vulnerabilities: Use tools like CISA's vulnerability scanning to find the "open windows" in your network before hackers do.
Email Security: Implement controls like SPF, DKIM, and DMARC to stop phishing emails from ever reaching your staff's inboxes.
Multi-Factor Authentication (MFA): If you aren't using MFA for remote access and email, you’re essentially leaving your front door wide open.
Basic Cybersecurity Training: Your staff is your strongest asset—or your weakest link. Regular training on how to spot a suspicious link is vital.
Strong Encryption: Ensure that ePHI is encrypted both when it’s sitting on a server and when it’s being sent to another provider.
Enhanced Goals: Maturing Your Defense
Once the basics are covered, your policy should move toward more sophisticated protections:
Asset Inventory: You can't protect what you don't know you have. This means keeping a live list of every laptop, server, and medical device on your network.
Network Segmentation: This is a big one. You should isolate your medical devices (IoMT) from your general office network. If a guest's laptop gets a virus on the "Guest Wi-Fi," you don't want it traveling to your MRI machine.
Incident Response Planning: Don't wait for a crisis to decide who to call. Use CISA Tabletop Exercise Packages to practice your response to a simulated ransomware attack.
Future-Proofing Your Policy Against Emerging Threats
The threat landscape is changing, and your healthcare cybersecurity policy needs to change with it. We are seeing a shift from "reactive" security to "proactive" resilience.
The Healthcare Cybersecurity Act of 2025
Recent legislative developments, such as the S. 1851 Bill Text for the Healthcare Cybersecurity Act of 2025, aim to strengthen the partnership between CISA and HHS. This bill proposes a dedicated CISA liaison at HHS to provide real-time threat intelligence and tailored resources for small and rural practices—which are often the most vulnerable.
The Rise of IoMT and Medical Device Security
The Internet of Medical Things (IoMT) is a double-edged sword. While connected pacemakers and infusion pumps improve care, they also introduce new vulnerabilities. Many of these devices were not designed with security in mind. Your policy must address procurement—ensuring new devices are "secure-by-design"—and decommissioning, making sure data is wiped before a device is retired.
Zero Trust Architecture
The old "castle and moat" approach to security (where you trust everyone inside the network) is dead. Modern policies are moving toward Zero Trust. In a Zero Trust environment, the system assumes every user and device is a potential threat. Access is only granted on a "least privilege" basis—meaning a billing clerk only sees billing data, not surgical records.
Even the European Union is getting in on the action with the European Action Plan for Hospitals, which focuses on establishing a pan-European support center and early warning systems. While we are based in Florida, these global trends often dictate the "best practices" that eventually become standard requirements here at home.
Frequently Asked Questions about Healthcare Cybersecurity Policy
What are the primary threats addressed by a healthcare cybersecurity policy?
A comprehensive policy is designed to defend against a variety of nasties. Ransomware is the most famous, but phishing remains the most common way hackers get in. We also address IoMT vulnerabilities (unsecured medical devices), insider threats (either malicious or accidental), and unauthorized access to sensitive databases. The goal of the policy is to prevent data exfiltration—where your patient data is stolen and sold on the dark web.
How does the HIPAA Security Rule align with a healthcare cybersecurity policy?
The HIPAA Security Rule provides the legal framework for your policy. It mandates the Confidentiality, Integrity, and Availability of ePHI. Your policy is the "how-to" guide for meeting these mandates. For example, HIPAA requires "Risk Analysis," and your policy defines that you will perform this analysis every 12 months. It also covers scalable safeguards and workforce training, ensuring that your security grows as your practice grows. You can find a detailed Summary of the HIPAA Security Rule on the official HHS website.
What role do federal agencies play in supporting sector resilience?
Agencies like CISA (Cybersecurity and Infrastructure Security Agency) and HHS (Health and Human Services) act as your "digital bodyguards." They provide threat intelligence through the Health Sector Cybersecurity Coordination Center (HC3), offer free vulnerability scanning, and provide technical assistance during an incident. They also facilitate incident coordination to ensure that if one hospital is hit, others are warned immediately.
Conclusion
Building a healthcare cybersecurity policy isn't just a box to check for an auditor; it's a commitment to your patients. When patients walk into your clinic or hospital, they trust you with their lives—and their most private information. A breach of that data is a breach of that trust.
At Compliance Cybersecurity Solutions (CCS), we believe that "Cyber Safety is Patient Safety." We help Florida-based healthcare providers stay resilient by aligning their IT infrastructure with HIPAA and NIST standards. Our proactive defense strategies ensure that you aren't just reacting to the latest threat, but are prepared for whatever comes next.
Don't wait for a $9 million wake-up call. Secure your organization with our healthcare cybersecurity expertise and let us help you keep your organization's vitals safe.